نتائج البحث عن ï؟½ï؟½ï؟½ï؟½ï؟½ï؟½ï؟½ï؟½ï؟½ ï؟½ï؟½ï؟½ï؟½ï؟½ï؟½ï؟½ï؟½
رواية الأسرة - با جين
(5)
لـِ: با جين
رواية الأسرة يتناول فيها الكاتب أسرة إقطاعية برجوازية كبيرة تمثل هذه الطبقة الوا
ثاني اثنين
(0)
لـِ: طه حامد الدليمي
كتاب - ثاني اثنين - للمؤلف : طه حامد الدليمي
هذه الرسالة تحتوي على ومضَاتٍ و
Etude de l’effet de salvia officinalis sur les variations de quelques paramètres du stress oxydatif chez la souris supplémentée en méthionine.
(2)
لـِ: غزيل سارة روابحية سعيدة
تحميل رسالة ماجستير بعنوان Etude de l’effet de salvia officinalis sur les variat
The self social networks and psychological well-being بعنوان
(2)
رسائل ماجستير ،رسائل دكتوراه في علم الاجتماع .pdf ( 54 ) :: The self social n
حقائق قرآنية
(0)
لـِ: بابا علي ابن الشيخ عمر القرداغي
في هذا الكتاب
مباحث أساسية دقيقة، وأفكار مهمة في فهم أمور الدين استفدت معظمها
مراصد الاطلاع على اسماء الامكنة والبقاع : v.2
(2)
لـِ: ياقوت بن عبد الله الحموي،, 1179?-1229, بجاوي، علي محمد،ابن عبد الحق، عبد المؤمن،, 1260-1338,
تحميل كتاب مراصد الاطلاع على اسماء الامكنة والبقاع : v.2 - رابط مباشر pdf
الناشر
تنوير الحوالك : 3 v. in 1
(5)
لـِ: سيوطي،, 1445-1505, مالك بن انس،-795, سيوطي،1445-1505,
تحميل كتاب تنوير الحوالك : 3 v. in 1 - رابط مباشر pdf
الناشر: مطبعة محمد علي صبي
Post-Diagnosis Changes In Dietary Patterns And Body Weight Among
(2)
رسائل ماجستير ،رسائل دكتوراه في الصحة العامة .pdf ( 246 ) :: Post-Diagnosis C
A phenomenological account of practices
(1)
رسائل ماجستير ،رسائل دكتوراه في الفلسفة .pdf ( 246 ) :: A phenomenological ac
موانع الميراث في الشريعة الاسلامية وتطبيقاتها في المحاكم الشرعية بقطاع غزة
(3)
رسائل ماجستير ،رسائل دكتوراه في الشريعة .pdf ( 45 ) :: رسالة ماجستير بعنوان _
أوديسا الشمال وقصص أخرى
(0)
لـِ: جاك لندن
رواية أوديسا الشمال وقصص أخرى للمؤلف جاك لندن
اللغة العربية والأدب -> الروايات
الاغتراب الوظيفي وعلاقته بسلوك المواطنة التنظيمية لدى العاملين في وزارة الاوقاف و الشئون الدينية
(26)
رسائل ماجستير, رسائل دكتوراة في الإدارة .pdf ( 593 ) :: رسالة ماجستير بعنوان
المنشآت الخشبية
(4)
لـِ: egyptsystem
كتاب - المنشآت الخشبية - للمؤلف : egyptsystem .
العلوم الطبيعية وا
بر الوالدين قيمة إسلامية عظيمة.pdf
(0)
تحميل كتيب بعنوان بر الوالدين قيمة إسلامية عظيمة.pdf كتيبات إسلاميةبدون حقوق للط
كتاب احترف فن الفراسة - ابراهيم الفقي
(2)
لـِ: ابراهيم الفقي
هل بالامكان معرفة ما يجول بخواطر الآخرين وفهم نفسياتهم وخبايا طويتهم، بحيث يغدون
كتاب الثورات العربية - نوال السعداوي
(1)
لـِ: نوال السعداوي
نوال السعداوي التي تطرَّقت إلى كل الموضوعات الساخنة والمحظورة والمثيرة للجدل على
Characterization and Bioassay of Different Commercial Products of B. thuringiensis Against Four Larval Stages and Adults of an Insect Tuta absoluta
(2)
أحدث رسائل ماجستير ،رسائل دكتوراه في العلوم.pdf ( 165 ) :: Characterization a
جهود الجامعة الاسلامية بغزة في نشر العقيدة الاسلامية
(1)
رسائل ماجستير ،رسائل دكتوراه في أصول الدين .pdf ( 141 ) :: رسالة ماجستير بعنو
Everything Changed Experiences of International Students Affected by a Home Country Crisis
(2)
رسائل ماجستير ،رسائل دكتوراه في ا?دارة التربوية .pdf ( 369 ) :: Everything Ch
ترميم المبانى
(0)
لـِ: elazhary2050
كتاب - ترميم المبانى - للمؤلف : elazhary2050 .
العلوم الطبيعية وال
البدوية
(1)
لـِ: إبراهيم رمزي
«البَدويَّة» فتاةٌ تَقطُن الصحراء، وتهيم حبًّا بابن عمها الذي يعشقها ويَسْتَرِق
مجموعة رسائل علمية مقبل بن هادي الوادعي
(0)
لـِ: مقبل بن هادي الوادعي
مجموعة رسائل علمية مقبل بن هادي الوادعي : يحتوي هذا الكتاب على مجموعةٍ من رسا
معجم رجال الحديث وتفصيل طبقات الرواة / juz 22
(3)
لـِ: خويي، ابو القاسم بن علي اكبر، -, 1899, طريحي، محمد سعيد،
تحميل كتاب معجم رجال الحديث وتفصيل طبقات الرواة / juz 22 - رابط مباشر pdf
الن
سعيد عقل.. وصفحة من ذاكرتي
(1)
صفحة من ذاكرتي.. هي الكلمة التي ألقيتها في الرابع من تموز سنة 2012 في المهرجان ا
كتاب أضغاث أقلام - أدهم الشرقاوى
(1)
لـِ: أدهم الشرقاوى
اقتباس » في الحب يتحدث الرجل عن انتصاراته وتتحدث المرأة عن هزائمها الرجل أجبن من
ديوان علي بن الجهم
(11)
لـِ: علي بن الجهم،, approximately 804-863, مردم، خليل،, 1895-1959, editor،
تحميل كتاب ديوان علي بن الجهم - رابط مباشر pdf
الناشر: المجمع العلمي العربي،
م
الميكانيكا الكلاسيكية: مقدمة أساسية
(0)
لـِ: مايكل كوهين
تُعنى الميكانيكا الكلاسيكية ببحث كيفية تحرُّك الأجسام عند تعرُّضها لقوى مختلفة،
مصباح الهدى في شرح العروة الوثقى. v.11
(3)
لـِ: املي، محمد تقي بن محمد،, 1886 or 7-,
تحميل كتاب مصباح الهدى في شرح العروة الوثقى. v.11 - رابط مباشر pdf
الناشر: publ
بيار ف. زيما - النص والمجتمع افاق علم اجتماع النقد
(2)
لـِ: بيار ف. زيما
تحميل كتاب بيار ف. زيما - النص والمجتمع افاق علم اجتماع النقد - رابط مباشر pdf
ط
Stability of career aspirations a test of Gottfredson's theory of circumscription and compromise
(1)
رسائل دكتوراة ،رسائل ماجسير في الارشاد وعلم النفس.pdf ( 696 ) :: Stability of
من عجائب الدعاء - خالد بن سليمان الربعي
(4)
تحميل كتاب من عجائب الدعاء - خالد بن سليمان الربعي - رابط مباشر pdf الزهد والرقا
أصحاب الرسول صلى الله عليه وسلم - محمود المصري
(6)
تحميل كتاب أصحاب الرسول صلى الله عليه وسلم - محمود المصري - رابط مباشر pdf السنة
الاخوان المسلمون ..احداث صنعت التاريخ..الجزء الثانى 1948-1952.pdf
(430)
تحميل كتاب الاخوان المسلمون ..احداث صنعت التاريخ..الجزء الثانى 1948-1952.pdf
مقالات ممنوعة
(0)
لـِ: سلامة موسى
هي مجموعة من المقالات المتنوعة التي كتبها سلامة موسى بأسلوب شيق وسلس، تناول خلال
السنة النبوية بين دعاة الفتنة وأدعياء العلم.pdf
(4)
تحميل كتاب السنة النبوية بين دعاة الفتنة وأدعياء العلم.pdf - رابط مباشر pdf
تاريخ الصحافة العراقية : v.1
(4)
لـِ: الحسني، عبد الرزاق،
تحميل كتاب تاريخ الصحافة العراقية : v.1 - رابط مباشر pdf
الناشر: مطبعة الغري،
البعد التطهيري الاتصالي
(2)
رسائل ماجستير ،رسائل دكتوراه في اللغة العربية .pdf ( 172 ) :: رسالة ماجستير ب
نهاية الارب فى فنون الادب v.11/12
(4)
لـِ: احمد بن عبد الوهاب النويرى،
تحميل كتاب نهاية الارب فى فنون الادب v.11/12 - رابط مباشر pdf
الناشر: دار الكتب
أبواب مختصرة في العقيدة.pdf
(2)
تحميل كتيب بعنوان أبواب مختصرة في العقيدة.pdf كتيبات إسلاميةبدون حقوق للطباعة وا
تحديد القيمة المبدئية للمشروع
(0)
لـِ: egyptsystem
كتاب - تحديد القيمة المبدئية للمشروع - للمؤلف : egyptsystem .
العل
The Impact of Ideology and Attorneys On Precedent Usage- An Analysis of State High Courts
(1)
رسائل ماجستير ،رسائل دكتوراه في العلوم السياسية .pdf ( 417 ) :: The Impact of
الإيمان والدين في القرآن-عبد السلام التونجي
(5)
تحميل كتاب الإيمان والدين في القرآن-عبد السلام التونجي - رابط مباشر pdf القرآن ا
مصحف دولة الكويت بخط الخطاط محمد سعد إبراهيم الحداد
(3)
تحميل كتاب مصحف دولة الكويت بخط الخطاط محمد سعد إبراهيم الحداد - رابط مباشر pdf
إفتراءات على الاسلام و المسلمين
(0)
لـِ: امير عبد العزيز
كتاب - إفتراءات على الاسلام و المسلمين - للمؤلف : امير عبد العزيز
الدين الإسل
Reading risk credit rating and the politics of municipal debt
(1)
رسائل ماجستير ،رسائل دكتوراة في الجغرافيا .pdf ( 253 ) :: Reading risk_ credi
Quantum Theory, Groups and Representations_ An Introduction (2017)
(1)
تحميل كتاب Quantum Theory, Groups and Representations_ An Introduction (2017) كت
كتاب بحث في المعنى والصدق - برتراند راسل
(5)
لـِ: برتراند راسل
كان الشغل الشاغل لبرتراند راسل متمثلاً في أسس المعرفة، وهو الموضوع الذي قاربه، ف
قصة النبي نوح عليه السلام في القرآن الكريم (دراسة تحليلية ستيلستيكية)
(2)
لـِ: ستي رملة
تحميل كتاب قصة النبي نوح عليه السلام في القرآن الكريم (دراسة تحليلية ستيلستيكية)
وحدة الامة الاسلامية في السنة النبوية
(3)
رسائل ماجستير ،رسائل دكتوراه في أصول الدين .pdf ( 393 ) :: رسالة ماجستير بعنو
الاقتصاد الإسلامي وأبعاده الأمنية
(1)
تحميل كتاب الاقتصاد الإسلامي وأبعاده الأمنية الإقتصاد - تحميل مباشر pdf
The Social Maze Navigating the Space Between Cultural Ideas and Social Action in an Urban World
(2)
رسائل ماجستير ،رسائل دكتوراه في علم الاجتماع .pdf ( 483 ) :: The Social Maze
احمد ديدات بين الانجيل والقرآن
(0)
لـِ: أحمد ديدات
كتاب - احمد ديدات بين الانجيل والقرآن - للمؤلف : أحمد ديدات
الدين الإسلامي ->
Loyalitä t und Lossagung im Islam
(0)
لـِ: Salih ibn Fawzan Al-Fawzan
Zu den Grundlagen der islamischen Glaubensinhalte geh?rt, dass sich der Muslim d
Inequality and Opportunity At theMsa-Level- Investigating Place بعنوان
(2)
رسائل ماجستير ،رسائل دكتوراه في علم الاجتماع .pdf ( 77 ) :: Inequality and Op
طبقات اعلام الشيعة، v.1pt.3
(4)
لـِ: اغا بزرك الطهراني، محمد محسن،
تحميل كتاب طبقات اعلام الشيعة، v.1pt.3 - رابط مباشر pdf
الناشر: المطبعة العلمية،
رواية المركيز جان /???????
(1)
لـِ: بورنيه، هنري ده،???????الفيكونت،???????, 1825-1901،, البشعلاني، اسطفان،???????, مترجم.???????,
تحميل كتاب رواية المركيز جان /??????? - رابط مباشر pdf
الناشر: المطبعة الكاثوليك
منهج الراغب الأصفهاني في كتاب المفردات
(20)
تحميل كتاب منهج الراغب الأصفهاني في كتاب المفردات - رسائل ماجستير ودكتوراه
معجم رجال الحديث وتفصيل طبقات الرواة / juz 9
(2)
لـِ: خويي، ابو القاسم بن علي اكبر، -, 1899, طريحي، محمد سعيد،
تحميل كتاب معجم رجال الحديث وتفصيل طبقات الرواة / juz 9 - رابط مباشر pdf
النا
فصل وتحديد منتجات الأيض الثانوي للمستخلص البوتانولي لنبات scoparium (Chenopodiaceae) Haloxylon "
(3)
رسائل ماجستير، رسائل دكتوراة في الكيمياء و الهندسة الكيميائية.pdf ( 82 ) :: ر
فتوح الغيب في الكشف عن قناع الريب وهو حاشية الطيبي على الكشاف
(5)
لـِ: الإمام شرف الدين حسين بن محمد بن عبد الله الطيبي (ت 743)
تحميل كتاب فتوح الغيب في الكشف عن قناع الريب وهو حاشية الطيبي على الكشاف - رابط
ضعيف الجامع الصغير وأحكامه
(2)
تحميل كتاب ضعيف الجامع الصغير وأحكامه - رابط مباشر pdf السنة والحديث الشريف
تقويم بكفيا الكبرى وتاريخ اسرها
(2)
لـِ: بليبل، ادمون،
تحميل كتاب تقويم بكفيا الكبرى وتاريخ اسرها - رابط مباشر pdf
الناشر: مطبعة العرائ
Technology Planning for Aligning Emerging Business Models and Regulatory Structures The Case of Electric Vehicle Charging and the Smart Grid
(1)
رسائل ماجستير ،رسائل دكتوراه في الادارة الهندسية .pdf ( 199 ) :: Technology P
صفوة الملح بشرح منظومة البيقوني في فن المصطلح ، محمد بن محمد البديري الدمياطي ، ت نور الدين طالب ، دار النوادر
(10)
تحميل كتاب صفوة الملح بشرح منظومة البيقوني في فن المصطلح ، محمد بن محمد البديري
المحرقة الصهيونية
(83)
فحص الشدات المعدنية
(0)
لـِ: elazhary2050
كتاب - فحص الشدات المعدنية - للمؤلف : elazhary2050 .
العلوم الطبيع
لمحات من تاريخ القراان
(2)
لـِ: اسنيقر، محمد علي،
تحميل كتاب لمحات من تاريخ القراان - رابط مباشر pdf
الناشر: دار المحيت،
مكان ال
كتاب المعتمد بن عَبَّاد: الملك الجواد الشجاع الشاعر المرزأ - عبد الوهاب عزام
(1)
لـِ: عبد الوهاب عزام
يعد «بنو عَبَّاد» أعظم ملوك الطوائف، وأفسحهم ملكًا، وأبعدهم صيتًا، وأكثرهم ذكرًا
اختراع موريل رواية لـ أدولفو بيوي كاساريس
(4)
تحميل كتاب اختراع موريل رواية لـ أدولفو بيوي كاساريس الادب العالمي والروايات - ت
السخرية البيانية في القرآن الكريم (دراسة موضوعية)
(9)
لـِ: محمد عدنان الخطيب
تحميل رسالة علمية السخرية البيانية في القرآن الكريم (دراسة موضوعية) - رابط مباشر
اثر استخدام المدخل البصري المكاني في تنمية بعض مهارات ما وراء المعرفة بالعلوم لدى طالبات الصف الثامن الاساسي
(11)
رسائل ماجستير, رسائل دكتوراة في مناهج وطرق التدريس .pdf ( 534 ) :: رسالة ماجس
تقريب البغية في ترتيب أحاديث الحلية دراسة وتخريج القسم الثاني من كتاب الأذان إلى نهاية الزكاة للإمام علي
(2)
تحميل كتاب تقريب البغية في ترتيب أحاديث الحلية دراسة وتخريج القسم الثاني من كتاب
التقويم والتمويل المصرفي للإستثمارات في الجزائر
(1)
تحميل كتاب التقويم والتمويل المصرفي للإستثمارات في الجزائر كتب في الإقتصاد - تح
منهجية المقال الفلسفي في الباكالوريا محمد الغنوشي والحبيب كتيتة
(2)
تحميل كتاب منهجية المقال الفلسفي في الباكالوريا محمد الغنوشي والحبيب كتيتة كتب ف
دور حركة الشبيبة الطلابية في تعزيز المشاركة السياسية في فلسطين 2004-2012
(1)
رسائل ماجستير ،رسائل دكتوراه في التخطيط والتنمية السياسية .pdf ( 50 ) :: رسال
السياق اللغوي وأثره في تعليمية اللغة
(8)
تحميل كتاب السياق اللغوي وأثره في تعليمية اللغة - رسائل ماجستير ودكتوراه
Handbook of differential equations. Stationary partial differential equations. Volume 3 North Holland (2006)
(1)
تحميل كتاب Handbook of differential equations. Stationary partial differential e
الدراسة اللغوية للقرآن عند تمام
(8)
تحميل كتاب الدراسة اللغوية للقرآن عند تمام - رسائل ماجستير ودكتوراه
اقرارات ناقصي الاهلية في الشريعة الاسلامية
(1)
رسائل ماجستير ، رسائل دكتوراة في التخصصات الاسلامية.pdf ( 163 ) :: رسالة ماجس
المسيحية و السيف...وثائق ابادة هنود القارة الامريكية على ايدي المسيحيين الاسبان - سلسلة من اجل الحقيقة ج2
(0)
لـِ: برتولومي دي لاس كازاس
كتاب - المسيحية و السيف...وثائق ابادة هنود القارة الامريكية على ايدي المسيحيين
تاريخ حرب البلقان الأولى: بين الدولة العلية والاتحاد البلقاني المؤلف من البلغار والصرب واليونان والجبل الأسود
(0)
لـِ: يوسف البستاني
كانت الإمبراطورية العثمانية في نهاية القرن التاسع عشر قد وصلت لحالة ملحوظة من ال
العقيدة الصحيحة وما يضادها (تايلندي)
(2)
تحميل كتاب العقيدة الصحيحة وما يضادها (تايلندي).pdf رابط مباشر كتب اسلامية
سفر السعادة
(6)
لـِ: فيروزابادي، محمد بن يعقوب،, 1329-1414 or 1415,
تحميل كتاب سفر السعادة - رابط مباشر pdf
الناشر: ادارة الطباعة المنيرية،
مكان ا
Wahai Saudari Muslimah Pakailah jilbabmu
(0)
لـِ: Abdullah bin Abdurrahman ad-Duwaisy
Menjelaskan pentingnya busana muslimah untuk menjaga kehormatan dan kemuliaan wa
الاستكمال لبيان جميع ما يأتي في كتاب الله عز وجل في مذهب القراء السبعة في التفخيم والإمالة وما كان بين اللفظين مُجملا كاملا
(0)
لـِ: الإمام أبو الطيب عبد المنعم بن عبيد الله بن غلبون الحلبي المقرئ (ت 389)
تحميل كتاب الاستكمال لبيان جميع ما يأتي في كتاب الله عز وجل في مذهب القراء السبع
Investigation of the use of ICT in the modernization of the health care sector
(2)
رسائل ماجستير, رسائل دكتوراة في الإدارة .pdf ( 1572 ) :: Investigation of the
الخصائص V.3
(7)
لـِ: ابن جني، ابو الفتح عثمان،, -1002, نجار، محمد علي،
تحميل كتاب الخصائص V.3 - رابط مباشر pdf
الناشر: دار الهدى للطباعة والنشر،
مكان
Three essays on location aspects in biotechnology entrepreneurship
(1)
رسائل ماجستير ،رسائل دكتوراه في الزراعة والاقتصاد الزراعي .pdf ( 248 ) :: Th
كتاب المنقذ قراءة لقلب افلاطون.pdf
(5)
تحميل كتاب كتاب المنقذ قراءة لقلب افلاطون.pdf - رابط مباشر pdf
اشكالات التنفيذ الموضوعية
(4)
تحميل كتاب اشكالات التنفيذ الموضوعية المكتبة القانونية - تحميل مباشر pdf
PREDICTION OF CALMODULIN-BINDING PROTEINS USING SHORT LINEAR MOTI
(3)
رسائل ماجستير ورسائل دكتوراة في علم الحاسوب.pdf ( 356 ) :: PREDICTION OF CALM
Excitable Signal Relay and Emergent Behavior in the Social Amoeba Dictyostelium discoideum
(0)
رسائل ماجستير ،رسائل دكتوراه في الفيزياء .pdf ( 314 ) :: Excitable Signal Rel
حقيقة دعوة التقريب
(0)
لـِ: بكر بن عبد الله أبو زيد
حقيقة دعوة التقريب : رسالة مختصرة للعلامة بكر أبو زيد - رحمه الله - ذكر فيها حقا
تامر طه بكر - السلفية بعيون غربية - ملون
(3)
لـِ: تامر طه بكر
تحميل كتاب تامر طه بكر - السلفية بعيون غربية - ملون - رابط مباشر pdf
طبعة مركز ا
Study of the Impact of Fertilization and Irrigation on Soil Chemical and Physical Properties under Different Cultivation Systems
(2)
رسائل ماجستير، رسائل دكتوراة في الكيمياء و الهندسة الكيميائية.pdf ( 1002 ) ::
حمزة بن حبيب الزيات وما انفرد به من قراءة
(9)
تحميل كتاب حمزة بن حبيب الزيات وما انفرد به من قراءة - رسائل ماجستير ودكتوراه
( 5 es ) اثر توظيف استراتيجية دورة في تنمية بعض عمليات العلم و التفكير الابداعي في العلوم لدى طلاب الصف الخامس الاساسي
(5)
رسائل ماجستير, رسائل دكتوراة في مناهج وطرق التدريس .pdf ( 428 ) :: ( 5 es ) ر
10 طرق لكسب الجيران.pdf
(4)
تحميل كتيب بعنوان 10 طرق لكسب الجيران.pdf كتيبات إسلاميةبدون حقوق للطباعة والنشر
شرح القواعد الحسان في تفسير القرآن
(2)
لـِ: الشيخ محمد بن صالح العثيمين (ت 1421)
تحميل كتاب شرح القواعد الحسان في تفسير القرآن - رابط مباشر pdf
تفسير القرآن -> أ
عرب ومسلمون للبيع
(0)
لـِ: عبد الودود شلبي
كتاب - عرب ومسلمون للبيع - للمؤلف : عبد الودود شلبي
الدين الإسلامي -> كتب إسل
رواية عودة الغائب - منذر القباني
(0)
لـِ: منذر القباني
الرواية تدور حول حدث دار قبل قرن من الزمان وما تبعه من محاولة فك طلاسم رسالة لنج
MICROFLUIDICS-BASED MICROGEL SYNTHESIS FOR IMMUNOISOLATION AND IMMUNOMODULATION IN PANCREATIC ISLET TRANSPLANTATION
(0)
رسائل ماجستير ،رسائل دكتوراه في الهندسة الميكانيكية .pdf ( 819 ) :: MICROFLUI
كتاب ضربة في قلبك - أحمد رجب
(1)
لـِ: أحمد رجب
الكاتب أراد من هذا الكتاب توصيل فكرة معينة الا وهي ان المرأة كائن اسطوري هدفه ال
حاشية الصبان على شرح الاشموني على الفية ابن مالك في النحو والصرف.
(4)
لـِ: صبان، محمد بن علي،, -1791 or 1792, اشموني، علي بن محمد،, 1435-1494 or 1495,
تحميل كتاب حاشية الصبان على شرح الاشموني على الفية ابن مالك في النحو والصرف. - ر
تعليقة الهيدجي على المنظومة وشرحها
(10)
لـِ: هيدجي، محمد علي،, -1927 or 1928,
تحميل كتاب تعليقة الهيدجي على المنظومة وشرحها - رابط مباشر pdf
الناشر: مؤسسة الا
فولفجانج ايسر ت عبدالوھاب علوب - فعل القراءة - نظرية في الاستجابة الجمالية
(3)
لـِ: فولفجانج ايسر ت عبدالوھاب علوب
تحميل كتاب فولفجانج ايسر ت عبدالوھاب علوب - فعل القراءة - نظرية في الاستجابة الج
تعلم html الجزء الثاني
(0)
لـِ: محمد رمزي حلمي
هذا هو الجزء الثاني من كتابي والجزء الاول موجود في الكتاب ف الجزء الثالث سيضم ال
Developing a Hierarchical Decision Model to Evaluate Nuclear Powe بعنوان
(2)
رسائل ماجستير ،رسائل دكتوراه في الادارة الهندسية .pdf ( 7 ) :: Developing a H
A ROADMAP TO SAFE AND RELIABLE ENGINEERED BIOLOGICAL NANO-COMMUNI
(3)
رسائل ماجستير ورسائل دكتوراة في علم الحاسوب.pdf ( 82 ) :: A ROADMAP TO SAFE A
المصحف الشريف المنسوب إلى عثمان بن عفان رضي الله عنه (نسخة متحف طوب قابي سرايي)
(17)
تحميل كتاب المصحف الشريف المنسوب إلى عثمان بن عفان رضي الله عنه (نسخة متحف طوب ق
التصوير البياني في حديث القرآن عن القرآن (دراسة بلاغية تحليلية)
(4)
لـِ: الدكتور عبد العزيز بن صالح بن عبد العزيز العمار
تحميل كتاب التصوير البياني في حديث القرآن عن القرآن (دراسة بلاغية تحليلية) - راب
Axioms of Set Theory and Equivalents of Axiom of Choice
(0)
رسائل ماجستير ،رسائل دكتوراة في الرياضيات.pdf ( 294 ) :: Axioms of Set Theory
[ Matrix Methods in Data Mining and Pattern Recognition (2007, Society for Industrial and Applied Mathematics)_2
(120)
تحميل كتاب [ Matrix Methods in Data Mining and Pattern Recognition (2007, Societ
Pillars of Faith
(0)
لـِ: Jafar Sheikh Idrees
Pillars of Faith: discusses the fundamentals of faith, by outlining and detailin
Quantum Ergodicity and the Analysis of Semiclassical Pseudodi?erential Operators
(0)
رسائل ماجستير ،رسائل دكتوراة في الرياضيات.pdf ( 345 ) :: Quantum Ergodicity a
افتراس اللحوم الآدمية: زيارة إلى التاريخ المقارن - أ. د. عبد العزيز غوردو
(12)
لـِ: أ. د. عبد العزيز غوردو
عنوان الكتاب:
افتراس اللحوم الآدمية
زيارة إلى التاريخ المقارن
تأليف:
أ. د. عبد
Analyse de fonctionnement de compresseur par l’application de l’AMDEC (compresseur de la mine de Boukhadra)
(0)
لـِ: Samet Henda Djrida Nabil
تحميل رسالة ماجستير بعنوان Analyse de fonctionnement de compresseur par l’applic
الصورة المدركة للمرشد التربوي في المدارس الحكومية في محافظة الخليل وعلاقتها بأدائه الوظيفي من وجهة نظر مديري المدارس
(5)
رسائل دكتوراة ،رسائل ماجسير في الارشاد وعلم النفس.pdf ( 603 ) :: رسالة ماجستي
روائع من أقوال الرسول صلى الله عليه وسلم
(1)
تحميل كتاب روائع من أقوال الرسول صلى الله عليه وسلم - رابط مباشر pdf السنة والحد
كتاب الشعور بما يحدث - أنطونيو داماسيو
(6)
لـِ: أنطونيو داماسيو
كتاب «الشعور بما يحدث» من الكتب ذات الشهرة الكبيرة فقد ترجم الكتاب الى سبع عشرة
the impact of the electronic press on the palestinian political development in palestine west bank gaza strip from 1996 up to 2007
(1)
رسائل ماجستير ،رسائل دكتوراه في التخطيط والتنمية السياسية .pdf ( 91 ) :: the_
DEVELOPMENT OF ERROR CORRECTION TECHNIQUES FOR NITRATE-N LOAD ESTIMATION MODELS
(1)
رسائل ماجستير ،رسائل دكتوراه في الهندسة الزراعة والزراعة ( 296 ) :: DEVELOPME
A Semester Course in Trigonometry
(1)
تحميل كتاب A Semester Course in Trigonometry كتب في الرياضيات - تحميل مباشر pdf
Development and Benchmarking of Cryptographic Implementations on Embedded Platforms
(1)
رسائل ماجستير ،رسائل دكتوراة في الهندسة الكهربائية .pdf ( 425 ) :: Developmen
قاموس المعين الألفاظ العسرة في الكتاب المقدس
(14)
تحميل كتاب قاموس المعين الألفاظ العسرة في الكتاب المقدس قواميس ومعاجم - تحميل مب
The Regulation Of Intervertebral Disc Cell Interactions With Their Surrounding Microenvironment
(2)
رسائل ماجستير ،رسائل دكتوراه في الهندسة الطبية والحيوية .pdf ( 490 ) :: The R
prevalence of urinary tract infection among children of primary schools in nablus
(2)
رسائل ماجستير ،رسائل دكتوراه في الصحة العامة .pdf ( 17 ) :: prevalence_of_uri
ACCESSING TRANSIT IN THE TOWER ROAD TRIANGLE AN EVALUATION OF THE BUILT ENVIRONMENT AND BUS STOP ACCESSIBILITY
(2)
رسائل ماجستير ،رسائل دكتوراه في التخطيط الحضري والاقليمي .pdf ( 63 ) :: ACCES
تحقيق التأدية المأمولة في اللغة والأدب
(8)
تحميل كتاب تحقيق التأدية المأمولة في اللغة والأدب - بحوث لغوية قصيرة
عبدالوھاب علوب - التراث - معجم انجليزي-عربي ويضم الفاظ الحضارة والتراث والفنون والاديان
(1)
لـِ: عبدالوھاب علوب
تحميل كتاب عبدالوھاب علوب - التراث - معجم انجليزي-عربي ويضم الفاظ الحضارة والترا
تجليات السرد في القصيدة الجاهلية
(20)
تحميل كتاب تجليات السرد في القصيدة الجاهلية - رسائل ماجستير ودكتوراه
Low Bandwidth Communication for Networked Power Hardware-In-The-Loop Simulation
(0)
رسائل ماجستير ، رسائل دكتوراه في الهندسة الالكترونية .pdf ( 52 ) :: Low Bandw
كتاب علم الفراسة الحديث - جُرجي زيدان
(1)
لـِ: جُرجي زيدان
«الفراسة عند العرب علم من العلوم الطبيعية تُعْرف به أخلاق الناس الباطنة من النظر
كتاب المرأة العربية (من العنف والتمييز إلى المشاركة السياسية) - مجموعة مؤلفين
(6)
لـِ: مجموعة مؤلفين
يقدم هذا الكتاب الذي ساهم فيه نخبة من الباحثين العرب، مجموعة دراسات تتمحور حول ق
اسرائيل البداية والنهاية
(1)
لـِ: مصطفى محمود
إن اسرائيل تتصرف وكأنها تتعامل مع أصفار وهى تتوسع وكأنها تمرح فى فراغ ، وهذا الغ
النجوم الزاهرة في ملوك مصر والقاهرة v.7
(1)
لـِ: ابن تغريبردي، ابو المحاسن يوسف،, 1411-1470,
تحميل كتاب النجوم الزاهرة في ملوك مصر والقاهرة v.7 - رابط مباشر pdf
الناشر: دار
David Young Computational chemistry_ a practical guide for applying techniques to real world problems Wiley (2001)
(2)
تحميل كتاب David Young Computational chemistry_ a practical guide for applying t
Examination of Steel Pin and Hanger Assembly Performance – Retrofit to Replacement
(2)
أحدث رسائل ما جستير ،رسائل دكتوراه الهندسة المدنية .pdf ( 215 ) :: Examinatio
الارضيات المرتفعة
(1)
لـِ: egyptsystem
كتاب - الارضيات المرتفعة - للمؤلف : egyptsystem .
العلوم الطبيعية
جوامع الاداب في أخلاق الانجاب
(1)
لـِ: جمال الدين الدمشقي
تحميل كتاب جوامع الاداب في أخلاق الانجاب.pdf رابط مباشر - تأليف: جمال الدين الد
حطة العمود او توقيع العمود اوالشدة الخشبية للعمود الخرسانى للمهندس حسن قنديل
(0)
لـِ: مهندس حسن قنديل
كتاب - حطة العمود او توقيع العمود اوالشدة الخشبية للعمود الخرسانى للمهندس حسن ق
إعجاز القرآن الكريم والقصة القرآنية المعجزة
(0)
لـِ: الدكتور محمد زمين
تحميل رسالة علمية إعجاز القرآن الكريم والقصة القرآنية المعجزة - رابط مباشر pdf
م
اطفال..كامل كيلاني..قصص اطفال..بطل اتينا.pdf
(276)
تحميل كتاب اطفال..كامل كيلاني..قصص اطفال..بطل اتينا.pdf
اثر تطبيق الادارة الالكترونية على كفاءة العمليات الادارية في مشروع مسح سجلات اللاجئين الفلسطينيين وكالة الغوث الدولية غزة
(9)
رسائل ماجستير, رسائل دكتوراة في الإدارة .pdf ( 726 ) :: رسالة ماجستير بعنوان
انشاء الحوائط من الالومنيوم و الزجاج الحوائط الستائرية
(7)
تحميل كتاب انشاء الحوائط من الالومنيوم و الزجاج الحوائط الستائرية كتب هندسة معما
الإخبار بأسباب نزول الأمطار
(0)
لـِ: عبد الله بن جار الله بن إبراهيم الجار الله
الإخبار بأسباب نزول الأمطار : نظرا لتأخر نزول الأمطار مما نتج عنه غور المياه وقل
فاعلية استخدام نموذج اديسون للتعليم في تنمية المفاهيم و مهارات التفكير التاملي في الرياضيات لدى طالبات الصف التاسع الاساسي بمحافظات رفح
(1)
رسائل ماجستير, رسائل دكتوراة في مناهج وطرق التدريس .pdf ( 243 ) :: رسالة ماجس
الالفين في امامة مولانا امير المؤمنين علي بن ابي طال
(6)
لـِ: ابن المطهر الحلي، الحسن بن يوسف،, 1250-1325,
تحميل كتاب الالفين في امامة مولانا امير المؤمنين علي بن ابي طال - رابط مباشر pdf
نيكولاس رويل ت عبدالوهاب علوب - الوان من التفكيكية - دليل للمستخدم - ط المركز القومي للترجمة
(3)
لـِ: نيكولاس رويل ت عبدالوهاب علوب
تحميل كتاب نيكولاس رويل ت عبدالوهاب علوب - الوان من التفكيكية - دليل للمستخدم -
كتاب المهرجان لاابن سينا.
(5)
تحميل كتاب كتاب المهرجان لاابن سينا. - رابط مباشر pdf الناشر: لجنة الاثار الوطني
Why do we pray?
(0)
لـِ: Suhaib Hasan
Book - Why do we pray? - author : Suhaib Hasan
الدين الإسلامي -> العبادات
Estimation Of Basic And Mission Benefit Of Condition-Based Mainte بعنوان
(2)
رسائل ماجستير ،رسائل دكتوراه في الهندسة الميكانيكية .pdf ( 15 ) :: Estimation
دراسات في الفلسفة اليونانية
(12)
تحميل كتاب دراسات في الفلسفة اليونانية كتب فلسفه ومنطق - تحميل مباشر pdf
الفضائل المحمدية التي فضله الله بها صلى الله عليه وسلم على جميع البرية
(3)
لـِ: نبهاني، يوسف بن اسماعيل،, 1849-1932
تحميل كتاب الفضائل المحمدية التي فضله الله بها صلى الله عليه وسلم على جميع البري
الحداثة والتواصل في الفلسفة النقدية المعاصرة
(4)
تحميل كتاب الحداثة والتواصل في الفلسفة النقدية المعاصرة كتب فلسفه ومنطق - تحميل
الباراسيكولوجية ملخصها وتطورها
(3)
تحميل كتاب الباراسيكولوجية ملخصها وتطورها باراسيكولوجي - تحميل مباشر pdf
حمايت از توحيد
(0)
لـِ: عبدالعزيز بن عبدالله بن باز
عقايد ناب و اصيل ديني را بيان کرده و مسلمانان را نسبت به بدعتها و خرافههاي دين
إستدراك وتعقيب على الشيخ الأرناؤوط في تأويله بعض آيات الصفات.pdf
(3)
تحميل كتاب إستدراك وتعقيب على الشيخ الأرناؤوط في تأويله بعض آيات الصفات.pdf - را
مدى تضمن كتب التربية الاسلامية للمرحلة الثانوية لقيمة التسامح وتصور مقتر ح لاثرائها
(3)
رسائل ماجستير, رسائل دكتوراة في مناهج وطرق التدريس .pdf ( 86 ) :: رسالة ماجست
ذكرى يوسف يعقوب مسكوني، 1903-1971
(2)
تحميل كتاب ذكرى يوسف يعقوب مسكوني، 1903-1971 - رابط مباشر pdf الناشر: مطبعة الجا
الإنسان يبحث عن المعنى لـ فيكتور فرانكل
(18)
تحميل كتاب الإنسان يبحث عن المعنى لـ فيكتور فرانكل كتب في علم النفس و الإجتماع -
فوشيه الشارتري..تاريخ الحملة إلى القدس.pdf
(315)
تحميل كتاب فوشيه الشارتري..تاريخ الحملة إلى القدس.pdf
واقع الثقافة التنظيمية في شركات المقاولات في قطاع غزة
(13)
رسائل ماجستير, رسائل دكتوراة في الإدارة .pdf ( 229 ) :: رسالة ماجستير بعنوان
الحركة النقدية حول الريادة في الشعر
(9)
تحميل كتاب الحركة النقدية حول الريادة في الشعر - رسائل ماجستير ودكتوراه
قضية مجيء المصدر المنكَّر حالاً في القرآن الكريم دراسة نحوية نقديةقضية مجيء المصدر المنكَّر حالاً في القرآن الكريم دراسة نحوية نقدية
(2)
تحميل كتاب قضية مجيء المصدر المنكَّر حالاً في القرآن الكريم دراسة نحوية نقديةقض
كتاب جنة عدم - أحمد عبد الحسين
(3)
لـِ: أحمد عبد الحسين
مجموعة شعرية تميّزت بشعرية عالية، وجمع بين الإحساس بالتاريخ وفجيعة الراهن، إضافة
Beberapa Nasehat Untuk Keluarga Muslim
(0)
لـِ: Yusuf bin Abdullah At Turki
Buku ini memuat nasehat kepada setiap individu dalam rumah tangga seorang muslim
كيفية عمل المحركات النفاثة
(4)
تحميل كتاب كيفية عمل المحركات النفاثة كتب الهندسة الميكانيكية - تحميل مباشر pdf
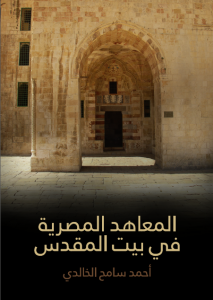
كتاب المعاهد المصرية في بيت المقدس - أحمد سامح الخالدي
(2)
لـِ: أحمد سامح الخالدي
في العصور الإسلامية الممتدة من حكم الفاطميين إلى حكم العلويين مرورًا بالأيوبيين
موقف مكي بن أبي طالب من القراءات المتواترة
(12)
تحميل كتاب موقف مكي بن أبي طالب من القراءات المتواترة - بحوث لغوية قصيرة
استخدام منهج سيجما ستة SIX SIGMAفي ضبط جودة التدقيق الداخلي
(4)
تحميل كتاب استخدام منهج سيجما ستة SIX SIGMAفي ضبط جودة التدقيق الداخلي كتب في ا
The Message -15
(0)
لـِ: United Muslims of Australia
Book - The Message -15 - author : United Muslims of Australia
الدين الإسلامي
إلى المتفكهين بالأعراض إلى الآمنين من مكر الله.pdf
(2)
تحميل كتيب بعنوان إلى المتفكهين بالأعراض إلى الآمنين من مكر الله.pdf كتيبات إسلا